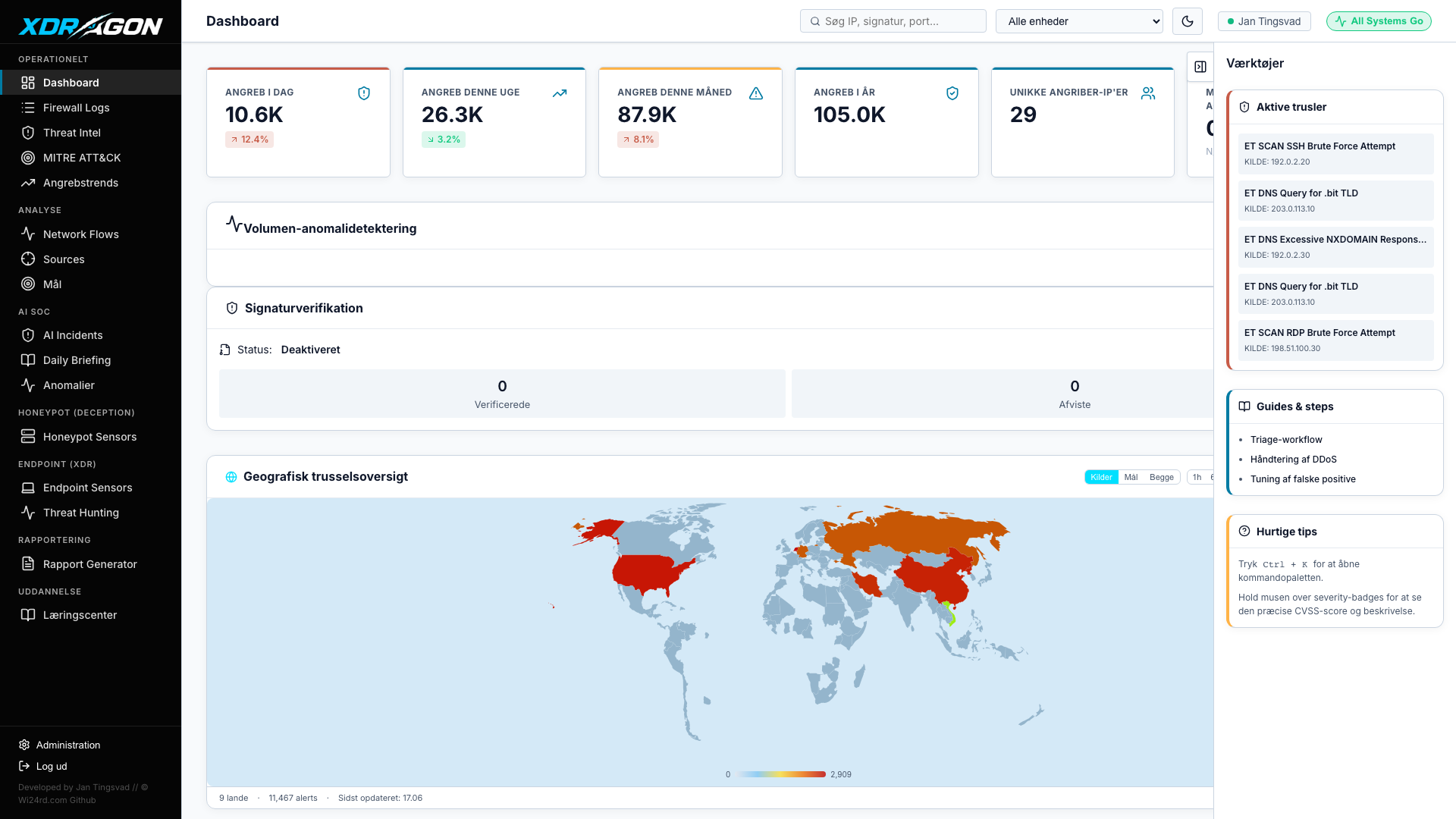
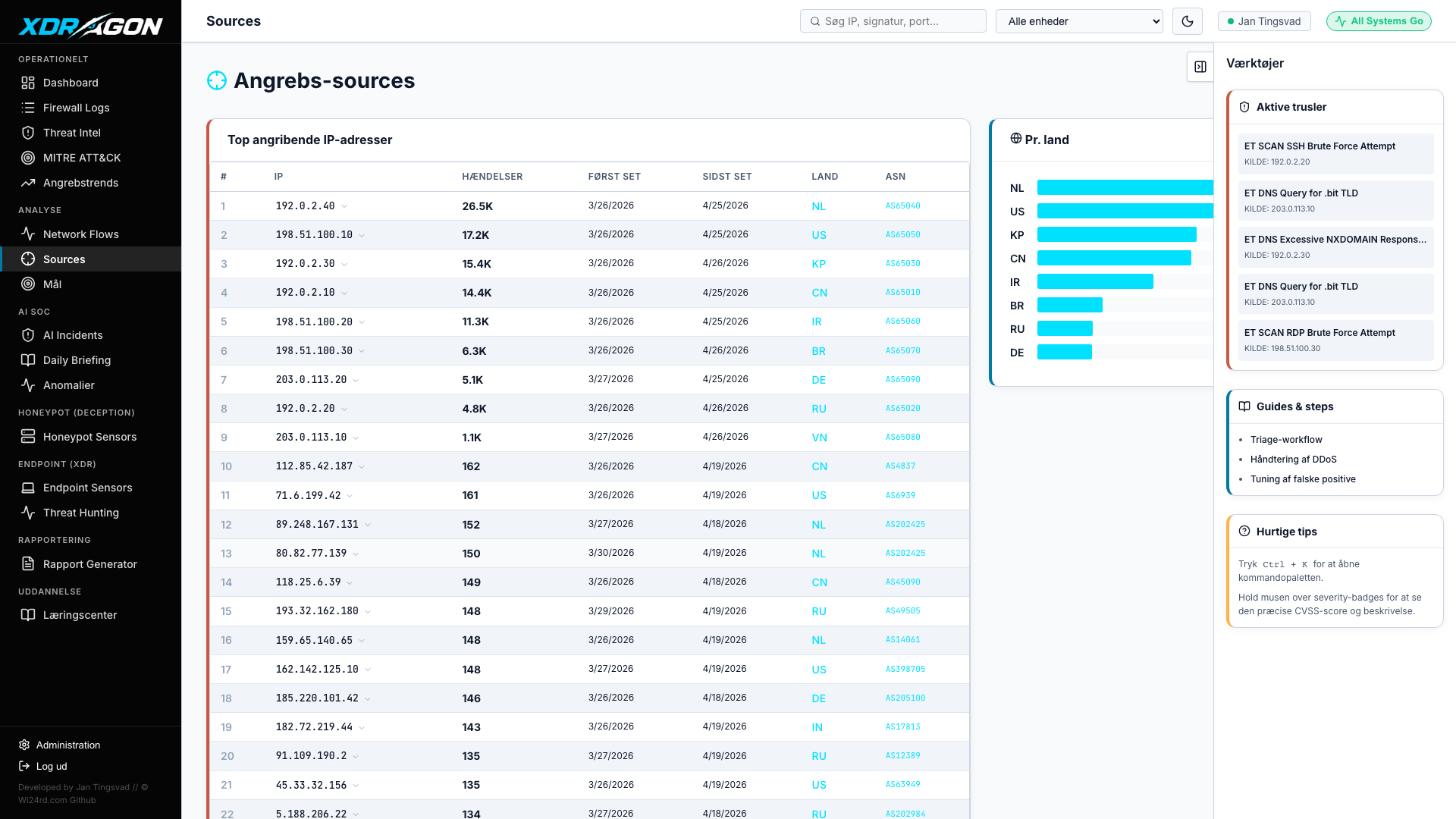
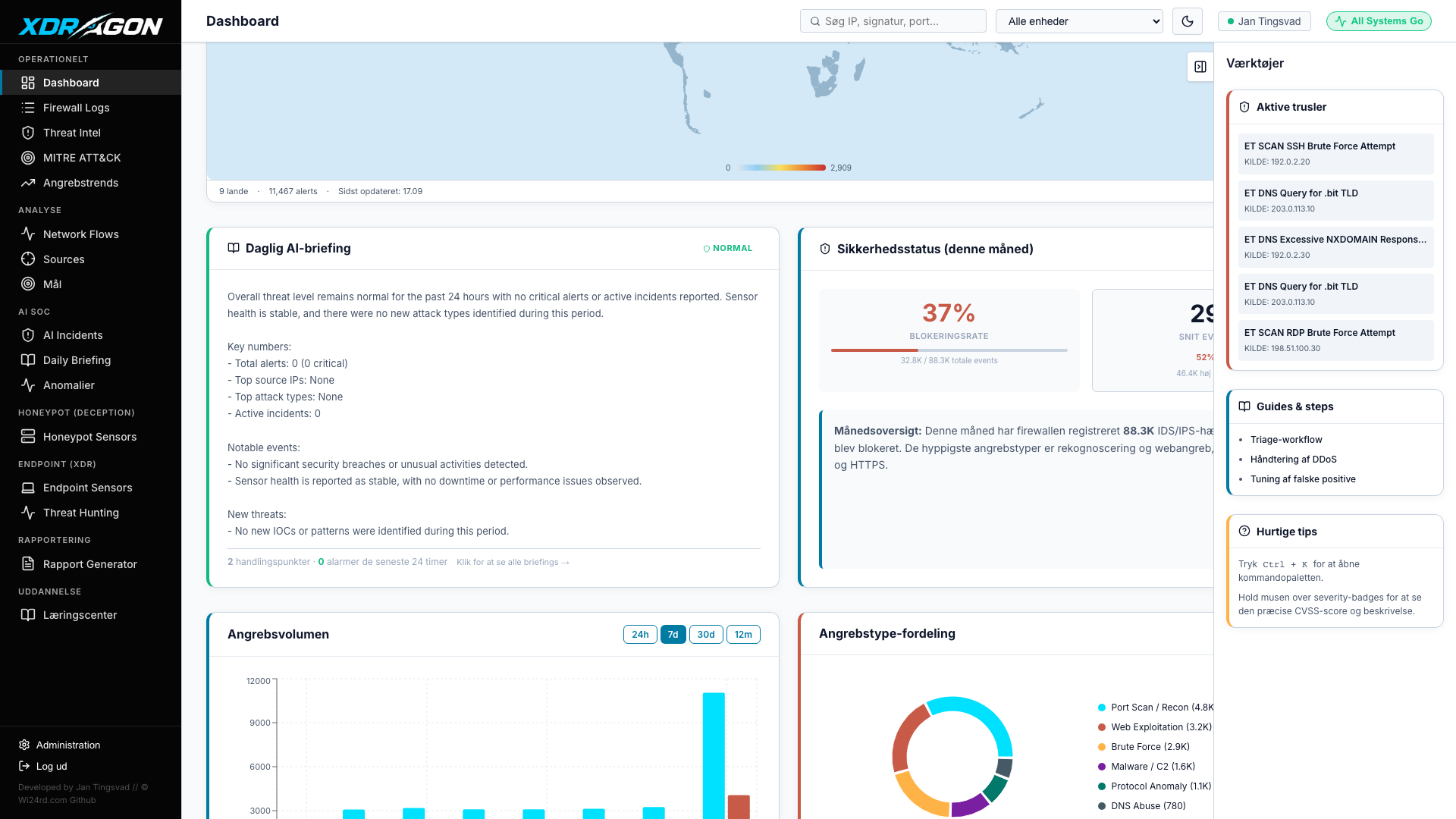
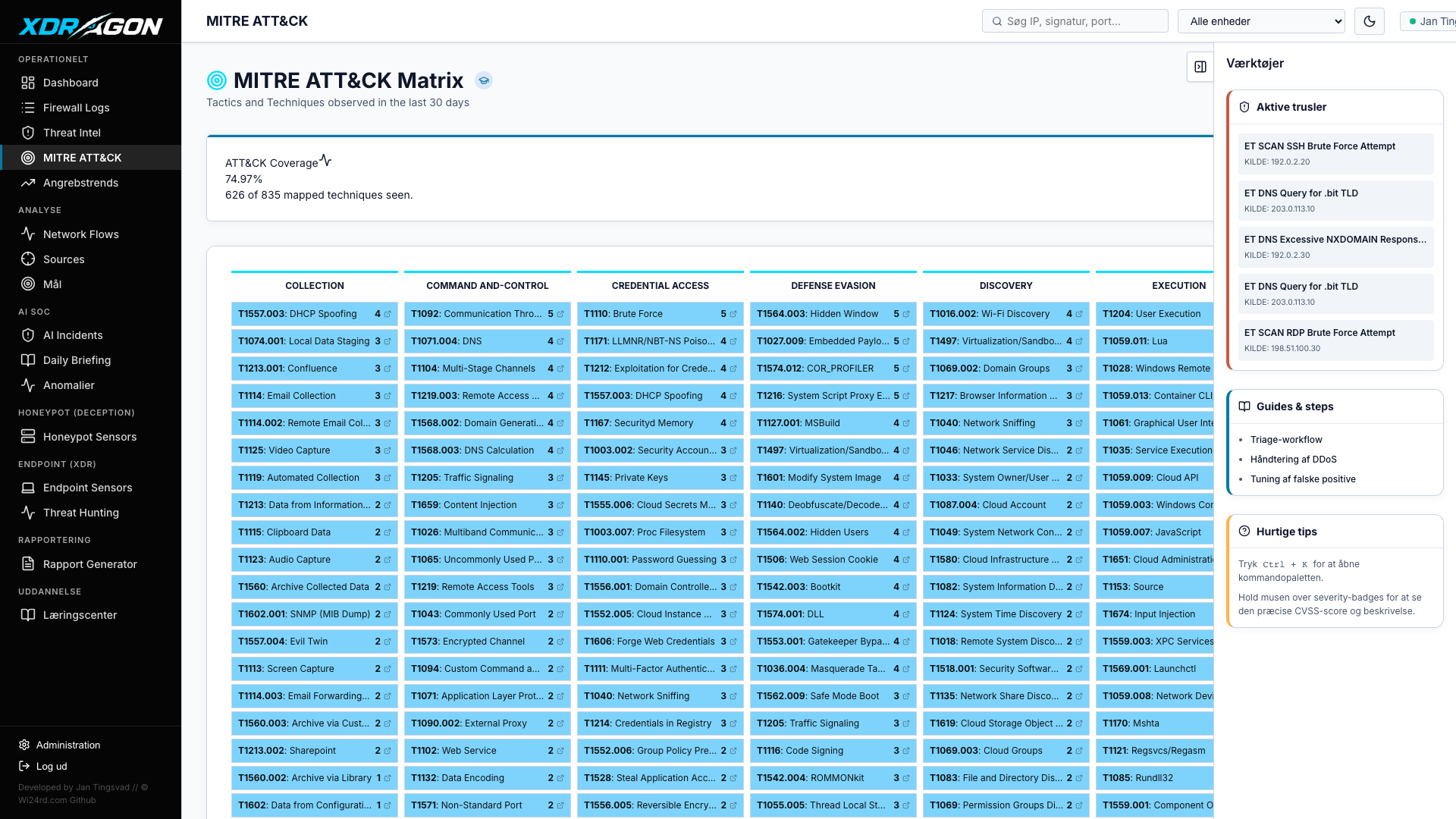
Visibility and control
from network to endpoint
T-SecOps combines real-time IDS/IPS monitoring, autonomous AI SOC operations, endpoint XDR, honeypot defense, and built-in NIS2 compliance — giving your security team complete situational awareness and decisive response capability, all hosted on your own infrastructure.