Your compliance posture.
Continuously scored.
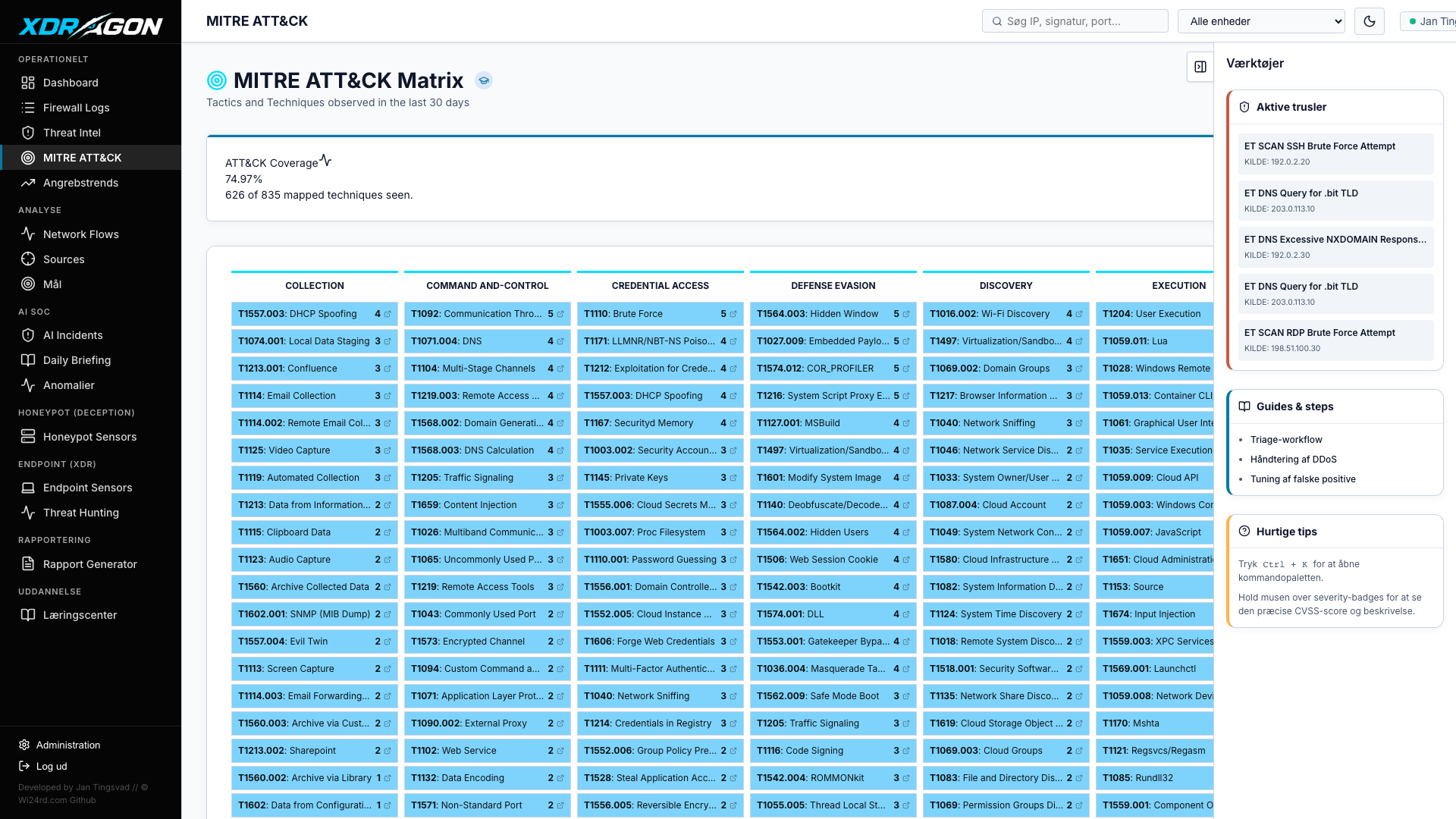
T-SecOps maps your live security telemetry directly to NIS2 Article 21, NIST CSF 2.0, and CIS Controls v8 — continuously. No manual worksheets. No consultant needed. Your compliance posture is scored, evidenced, and audit-ready at all times.
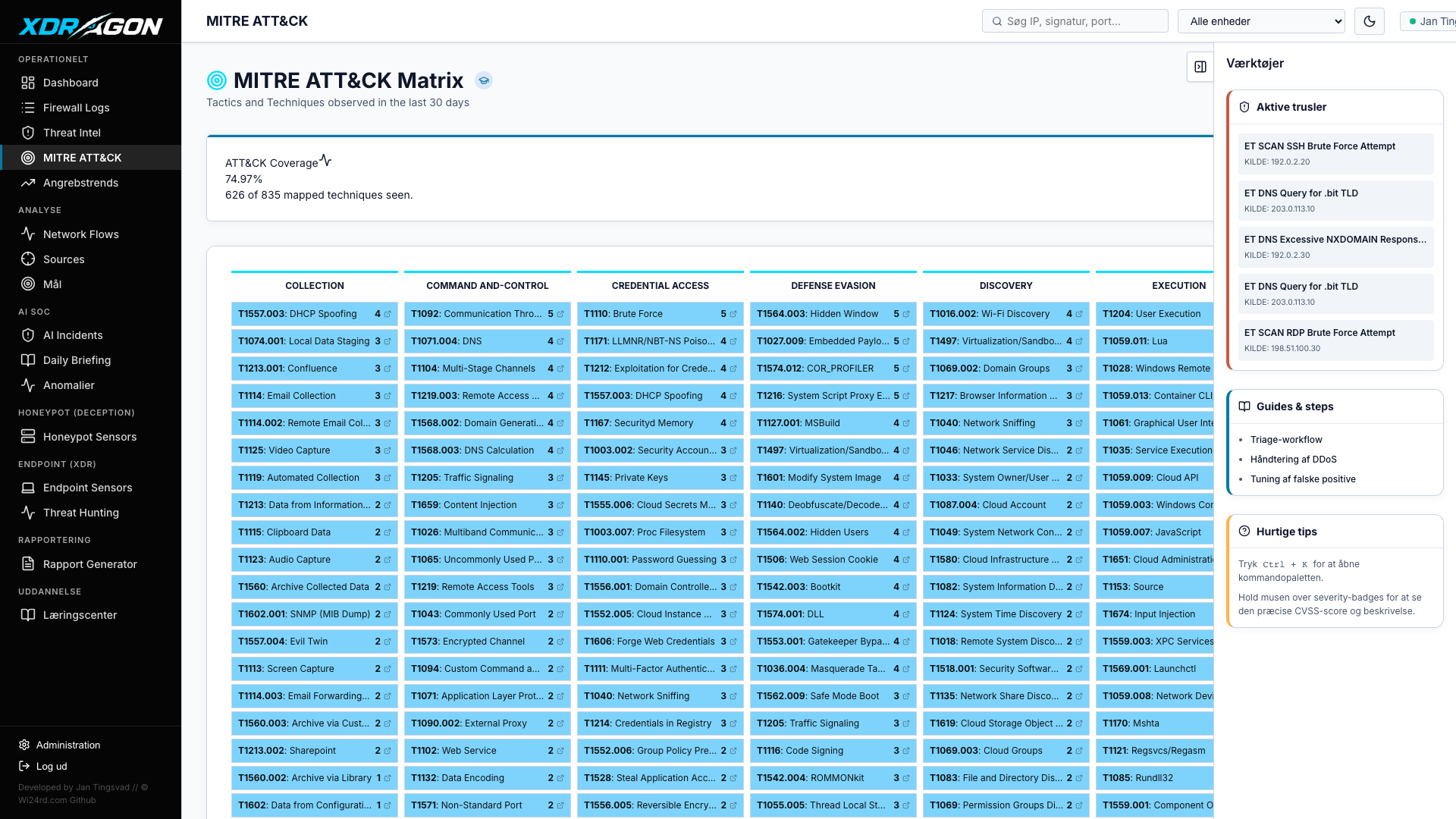
T-SecOps maps your live security posture to three major compliance frameworks simultaneously. Controls are auto-scored from your existing telemetry — no additional data collection required.
For every compliance gap, T-SecOps' AI advisor analyses your actual security telemetry — your network traffic patterns, your endpoint events, your specific vulnerabilities — and produces a remediation plan that makes sense for your environment.
Deploy T-SecOps and have your NIS2, NIST, and CIS compliance scoring live within the hour — no manual setup required.